

6
Mastering Linux Privilege Escalation is one of the most important skills for passing the OSCP exam, succeeding in penetration testing, and defending real-world Linux systems against attacks.
This guide breaks down the techniques taught in the course Linux Privilege Escalation Examples From Zero to Hero – OSCP, offering a structured overview of 30+ escalation vectors, practical examples, and defensive strategies.
🎥 Video Breakdown — Full Privilege Escalation Course
(Placed after introduction as per your global template)
Watch the full course here:
https://youtu.be/HfkMQ8wFBPE
✅ What Is Linux Privilege Escalation?
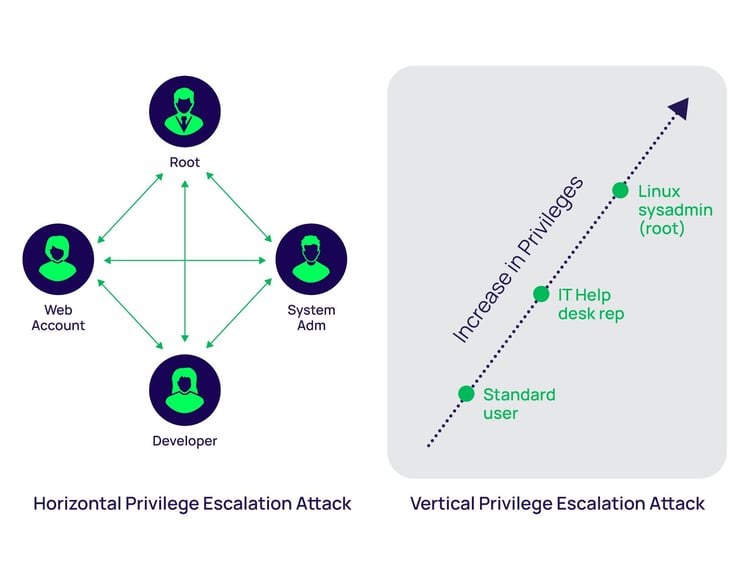
Linux privilege escalation involves exploiting misconfigurations, vulnerable applications, or weak permissions to gain higher-level access—often root.
Attackers use privilege escalation to:
- Access restricted files
- Run administrative commands
- Extract credentials
- Deploy backdoors or malware
Understanding these attack paths is crucial not only for pentesting but also for hardening Linux systems.
🔥 1. Environment Setup & Essential Linux Foundations
Before diving into exploitation, the course covers foundational steps every hacker must know:
✔ Setting Up Ubuntu Server
Learn how to deploy a secure VM for training using VirtualBox.
✔ Networking & SSH Access
Configure network interfaces and connect through secure shell for remote exploitation.
✔ Understanding the Linux CLI
Master commands needed to navigate, enumerate, and escalate privileges.
You learn:
- File permissions
- Ownership
- Shell operations
- Process management
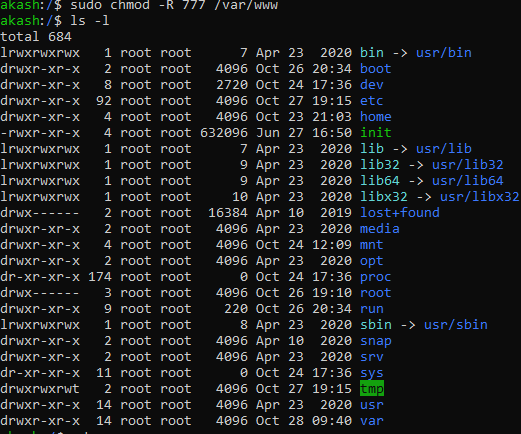
🔥 2. Exploiting Misconfigured File Permissions
Permissions are one of the most common privilege escalation vectors.
This course includes real examples such as:
✔ Bad Permissions on /etc/passwd
If writable by non-root users, attackers can replace hashed passwords.
✔ Readable /etc/shadow
A catastrophic misconfiguration—hackers can extract hashed passwords and crack them using tools like Hashcat.
✔ RWXRWXRWX (777) Group Exploits
Learn how to detect and exploit globally writable sensitive files.
✔ Finding Permission Weaknesses
Use enumeration tools to locate files that expose privilege escalation paths.

🔥 3. SUID-Based Privilege Escalation
SUID (Set User ID) allows binaries to run with root privileges—a goldmine for attackers.
✔ Understanding SUID
How Linux executes SUID binaries and why they can allow privilege jumps.
✔ Real Examples
- SUID misconfigured binaries
- Using editors like nano and vim to spawn root shells
- Exploiting
cp,bash, Python, Perl, awk, SED for privilege escalation
✔ How to Find SUID Files
Easily locate vulnerable binaries using:
find / -perm -4000 -type f 2>/dev/null
🔥 4. SUDO Misconfigurations
The SUDO mechanism is often misconfigured, allowing escalation without password prompts.
Examples covered:
- Running restricted commands as root
- Escalating through editors like vim, less
- File manipulation through sudo-enabled binaries
- Sudo -l enumeration techniques
If a user can run a command as root, that command can often be used to break out into a root shell.
🔥 5. Cron Job Privilege Escalation
Incorrectly configured crontab tasks allow attackers to replace or modify scripts executed automatically by the system.
Topics include:
- Writable scheduled scripts
- Environment manipulation
- Timing attacks
- Persistence techniques
🔥 6. Automated Enumeration: LinPEAS & LinSecurity
Two powerful tools explored in the course:
✔ LinPEAS
Scans the system for 100+ privilege escalation vectors instantly.
✔ LinSecurity
A step-by-step learning environment to practice real misconfigurations including:
- Sudo
- SUID
- Hashes in
/etc/passwd - Root squashing
- Docker privilege escalation
🔥 7. Docker Privilege Escalation
Misconfigured Docker environments can grant attackers immediate root-level access.
You learn:
- How Docker mounts expose the host
- Common misconfigurations
- Spawning a root shell through Docker
- How to avoid these mistakes in production systems


🔥 8. Password Cracking & Post-Exploitation
Once elevated privileges are gained, attackers often:
- Extract password hashes
- Crack them using Hashcat
- Perform lateral movement
- Establish persistence
The course gives hands-on examples of cracking weak passwords and replacing authentication entries.
🎯 Who Should Learn Linux Privilege Escalation?
This course is ideal for:
- 🟢 OSCP students
- 🟢 Ethical hacking learners
- 🟢 Pentesters & Red Teamers
- 🟢 Cybersecurity professionals
- 🟢 Anyone who wants to detect & prevent privilege escalation attacks
🎥 Watch the Full Training
(Second placement—before conclusion as required)
https://youtu.be/HfkMQ8wFBPE
🛡️ How to Prevent Privilege Escalation
Defense strategies covered include:
- Proper file permissions
- Hardening sudo configurations
- Auditing cron jobs
- Regular security updates
- Docker isolation best practices
- Strong password policies
- Log monitoring and detection
A complete checklist is also provided in the course to help secure Linux systems.
⭐ Conclusion: Master OSCP-Level Linux Privilege Escalation
Mastering Linux privilege escalation is essential for both offensive and defensive cybersecurity roles.
This course provides practical, step-by-step demonstrations of over 30 real-world techniques, making it perfect preparation for the OSCP exam and professional pentesting projects.
If you’re serious about cybersecurity, this is one of the most valuable skill sets you can learn.


